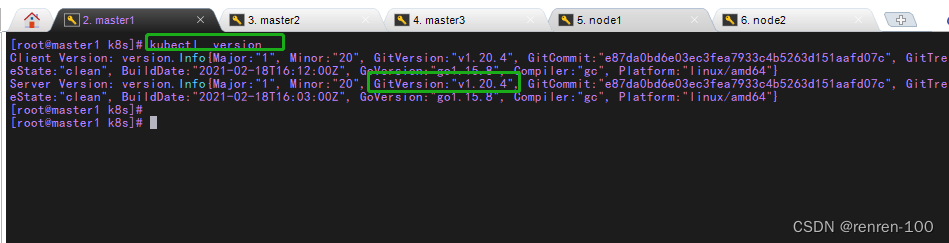
k8s 1.20 二进制安装

安装前的准备
CentOS Linux release 7.3.1611 (Core)
初始化系统参数
集群规划
192.168.6.20 master1 - etcd、kube-apiserver、kube-controller-manager、kube-scheduler
192.168.6.21 master2 - etcd、kube-apiserver、kube-controller-manager、kube-scheduler
192.168.6.22 master3 - etcd、kube-apiserver、kube-controller-manager、kube-scheduler
192.168.6.30 node1
192.168.6.31 node2
a, 系统环境设置
# 更换阿里源
yum -y install wget
mv /etc/yum.repos.d/CentOS-Base.repo /etc/yum.repos.d/CentOS-Base.repo.backup
wget -O /etc/yum.repos.d/CentOS-Base.repo http://mirrors.aliyun.com/repo/Centos-7.repo
sed -i 's#enabled=1#enabled=0#g' /etc/yum.repos.d/CentOS-Media.repo
yum clean all && yum makecache # centos7 更换阿里epel源
wget -O /etc/yum.repos.d/epel.repo http://mirrors.aliyun.com/repo/epel-7.repo
# 安装wget vim net-tools
yum -y install wget vim net-tools # 关闭selinux
sed -i 's#SELINUX=enforcing#SELINUX=disabled#g' /etc/selinux/config
setenforce 0
systemctl stop firewalld && systemctl disable firewalld# 网络管理
systemctl stop network
systemctl disable network
b,主机名称
hostnamectl set-hostname master1
hostnamectl set-hostname master2
hostnamectl set-hostname master3
hostnamectl set-hostname node1
hostnamectl set-hostname node2
c, 升级内核
rpm -ivh kernel-ml-6.1.10-1.el7.elrepo.x86_64.rpm#修改配置文件使新安装的内核成为默认启动选项
# GRUB_DEFAULT=saved
vim /etc/default/grub
GRUB_DEFAULT=0
# 执行命令:
grub2-mkconfig -o /boot/grub2/grub.cfg
d, 安装ipvsadm
yum -y install ipvsadm ipset sysstat conntrack libseccomp
e, 设置ipvs模块
cat << EOF > /etc/sysconfig/modules/k8s.modulesmodprobe -- ip_vsmodprobe -- ip_vs_rrmodprobe -- ip_vs_wrrmodprobe -- ip_vs_shmodprobe -- nf_conntrackmodprobe -- ip_tablesmodprobe -- ip_setmodprobe -- xt_setmodprobe -- ipt_setmodprobe -- ipt_rpfiltermodprobe -- ipt_REJECTmodprobe -- ipip
EOF
f, 是配置生效
source /etc/sysconfig/modules/k8s.modules
lsmod | grep -e ip_vs -e nf_conntrack
g,优化内核参数
cat <<EOF > /etc/sysctl.d/K8S.conf
net.ipv4.ip_forward=1
net.bridge.bridge-nf-call-iptables=1
fs.may_detach_mounts = 1
vm.overcommit_memory=1
vm.panic_on_oom=0
fs.inotify.max_user_watches=524288
fs.file-max=52706963
fs.nr_open=52706963
net.netfilter.nf_conntrack_max=2310720net.ipv4.tcp_keepalive_time=600
net.ipv4.tcp_keepalive_intvl=30
net.ipv4.tcp_keepalive_probes=10
net.ipv4.tcp_max_tw_buckets=36000
net.ipv4.tcp_tw_reuse = 1
net.ipv4.tcp_max_orphans = 327680
net.ipv4.tcp_orphan_retries = 3
net.ipv4.tcp_syncookies =1
net.ipv4.tcp_max_syn_backlog = 16384
net.ipv4.ip_conntrack_max = 65536
net.ipv4.tcp_timestamps = 0
net.core.somaxconn =16384
EOF
sysctl --system
h, 系统时间同步
chronyc sources -v
systemctl status chronyd
test
i, 设置hosts
192.168.6.20 master1
192.168.6.21 master2
192.168.6.22 master3
192.168.6.30 node1
192.168.6.31 node2
安装docker
test
cfssl 证书(master1节点上)
#选择master进行,也可选择其他wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64
# 下载的会比较慢
chmod +x cfssl_linux-amd64 cfssljson_linux-amd64 cfssl-certinfo_linux-amd64
mv cfssl_linux-amd64 /usr/local/bin/cfssl
mv cfssljson_linux-amd64 /usr/local/bin/cfssljson
mv cfssl-certinfo_linux-amd64 /usr/bin/cfssl-certinfo上传到/usr/bin/下
[root@master1 ~]# chmod +x /usr/bin/cfssl*
etcd 集群安装
a, 生成etcd证书
-------------------------master1节点------------------------
1)自签证书颁发机构(CA)
# 生成etcd 证书
mkdir -p ca/etcd
cd ca/etcd
#自签CA
[root@k8s-master1 etcd]# vim ca-config.json
{"signing": {"default": {"expiry": "87600h"},"profiles": {"www": {"expiry": "87600h","usages": ["signing","key encipherment","server auth","client auth"]}}}
}[root@k8s-master1 etcd]# vim ca-csr.json
{"CN": "etcd CA","key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "Beijing","ST": "Beijing"}]
}#生成证书
[root@k8s-master1 etcd]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -2)使用自签CA签发Etcd HTTPS证书
#创建证书申请文件
[root@k8s-master1 etcd]# vim server-csr.json
{"CN": "etcd","hosts": ["192.168.6.20","192.168.6.21","192.168.6.22","192.168.6.30","192.168.6.31"],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing"}]
}*注:上述文件hosts字段中IP为所有etcd节点的集群内部通信IP,一个都不能少!为了方便后期扩容可以多写几个预留的IP#生成证书
[root@k8s-master1 etcd]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server
b, 下载etcd 安装包并解压
wget https://mirrors.huaweicloud.com/etcd/v3.4.9/etcd-v3.4.9-linux-amd64.tar.gz-------------------------master1节点------------------------#创建工作目录并解压二进制包
[root@master1 ~]# mkdir -p /opt/etcd/{bin,cfg,ssl}
[root@master1 ~]# tar zxvf etcd-v3.4.9-linux-amd64.tar.gz
[root@master1 ~]# mv etcd-v3.4.9-linux-amd64/{etcd,etcdctl} /opt/etcd/bin/#创建etcd配置文件
[root@master1 ~]# vim /opt/etcd/cfg/etcd.conf
#[Member]
ETCD_NAME="etcd1"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.6.20:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.6.20:2379"#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.6.20:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.6.20:2379"
ETCD_INITIAL_CLUSTER="etcd1=https://192.168.6.20:2380,etcd2=https://192.168.6.21:2380,etcd3=https://192.168.6.22:2380,etcd4=https://192.168.6.30:2380,etcd5=https://192.168.6.31:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"*参数解释
• ETCD_NAME:节点名称,集群中唯一
• ETCD_DATA_DIR:数据目录
• ETCD_LISTEN_PEER_URLS:集群通信监听地址
• ETCD_LISTEN_CLIENT_URLS:客户端访问监听地址
• ETCD_INITIAL_ADVERTISE_PEERURLS:集群通告地址
• ETCD_ADVERTISE_CLIENT_URLS:客户端通告地址
• ETCD_INITIAL_CLUSTER:集群节点地址
• ETCD_INITIALCLUSTER_TOKEN:集群Token
• ETCD_INITIALCLUSTER_STATE:加入集群的当前状态,new是新集群,existing表示加入已有集群#systemd管理etcd
[root@master1 ~]# vim /usr/lib/systemd/system/etcd.service
[Unit]
Description=Etcd Server
After=network.target
After=network-online.target
Wants=network-online.target[Service]
Type=notify
EnvironmentFile=/opt/etcd/cfg/etcd.conf
ExecStart=/opt/etcd/bin/etcd \\
--cert-file=/opt/etcd/ssl/server.pem \\
--key-file=/opt/etcd/ssl/server-key.pem \\
--peer-cert-file=/opt/etcd/ssl/server.pem \\
--peer-key-file=/opt/etcd/ssl/server-key.pem \\
--trusted-ca-file=/opt/etcd/ssl/ca.pem \\
--peer-trusted-ca-file=/opt/etcd/ssl/ca.pem \\
--logger=zap
Restart=on-failure
LimitNOFILE=65536[Install]
WantedBy=multi-user.target#拷贝刚才生成的证书
[root@master1 ~]# cp ~/ca/etcd/*.pem /opt/etcd/ssl#将上面Master节点所有生成的文件拷贝到节点master2和节点master3上
[root@master1 ~]# scp -r /opt/etcd/ master2:/opt/
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service master2:/usr/lib/systemd/system/
[root@master1 ~]# scp -r /opt/etcd/ master3:/opt/
[root@master1 ~]# scp /usr/lib/systemd/system/etcd.service master3:/usr/lib/systemd/system/
其他节点 也是相同的,下面其他节点etcd集群也要一样#在节点master2和节点master3分别修改etcd.conf配置文件
[root@k8s-master2 ~]# vim /opt/etcd/cfg/etcd.conf
#[Member]
ETCD_NAME="etcd2"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.6.21:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.6.21:2379"#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.6.21:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.6.21:2379"
ETCD_INITIAL_CLUSTER="etcd1=https://192.168.6.20:2380,etcd2=https://192.168.6.21:2380,etcd3=https://192.168.6.22:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"[root@k8s-master2 ~]# vim /opt/etcd/cfg/etcd.conf
#[Member]
ETCD_NAME="etcd3"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.6.22:2380"
ETCD_LISTEN_CLIENT_URLS="https://192.168.6.22:2379"#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.6.22:2380"
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.6.22:2379"
ETCD_INITIAL_CLUSTER="etcd1=https://192.168.6.20:2380,etcd2=https://192.168.6.21:2380,etcd3=https://192.168.6.22:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"---------------master1、master2、master3节点------------------#启动并设置开机启动
systemctl daemon-reload
systemctl enable etcd
systemctl start etcd*注:master如果先启动了,会出现start悬停等待的现象,这时候可以先把node1、node2的etcd启动,随后master的etcd会正常启动。#查看集群状态
[root@master1 ~]# ETCDCTL_API=3 /opt/etcd/bin/etcdctl --cacert=/opt/etcd/ssl/ca.pem --cert=/opt/etcd/ssl/server.pem --key=/opt/etcd/ssl/server-key.pem --endpoints="https://192.168.6.20:2379,https://192.168.6.21:2379,https://192.168.6.22:2379" endpoint health --write-out=table
+---------------------------+--------+-------------+-------+
| ENDPOINT | HEALTH | TOOK | ERROR |
+---------------------------+--------+-------------+-------+
| https://10.8.165.101:2379 | true | 8.280002ms | |
| https://10.8.165.102:2379 | true | 8.113125ms | |
| https://10.8.165.103:2379 | true | 17.479134ms | |
+---------------------------+--------+-------------+-------+如果输出上面信息,就说明集群部署成功。
如果有问题第一步先看日志:/var/log/message 或 journalctl -u etcd# 添加别名, 永久生效
# 在执行etcdctl命令时需要指定认证授权文件, 所以将认证授权步骤 别名至 etcdctl 简化操作cd /etc/profile.d
vim etcd.sh
# 指定ETCDCTL_API版本为3
export ETCDCTL_API=3
# 创建etcdctl别名,指定监听地址,和证书
alias etcdctl='/opt/etcd/bin/etcdctl --cacert=/opt/etcd/ssl/ca.pem --cert=/opt/etcd/ssl/server.pem --key=/opt/etcd/ssl/server-key.pem --endpoints="https://192.168.6.20:2379,https://192.168.6.21:2379,https://192.168.6.22:2379"'source etcd.sh# 查看etcd集群的成员节点
etcdctl member list -w table
# 查看etcd集群节点状态 `在这里插入代码片`etcdctl endpoint status -w table## 查看集群健康状态etcdctl endpoint health -w tablenode1\\node2 安装docker
# step 1: 安装必要的一些系统工具
sudo yum install -y yum-utils device-mapper-persistent-data lvm2
# Step 2: 添加软件源信息
sudo yum-config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
# Step 3
sudo sed -i 's+download.docker.com+mirrors.aliyun.com/docker-ce+' /etc/yum.repos.d/docker-ce.repo
# Step 4: 更新并安装Docker-CE
sudo yum makecache fast
sudo yum -y install docker-ce
# Step 4: 开启Docker服务
sudo service docker start# 注意:
# 官方软件源默认启用了最新的软件,您可以通过编辑软件源的方式获取各个版本的软件包。例如官方并没有将测试版本的软件源置为可用,您可以通过以下方式开启。同理可以开启各种测试版本等。
# vim /etc/yum.repos.d/docker-ce.repo
# 将[docker-ce-test]下方的enabled=0修改为enabled=1
#
# 安装指定版本的Docker-CE:
# Step 1: 查找Docker-CE的版本:
# yum list docker-ce.x86_64 --showduplicates | sort -r
# Loading mirror speeds from cached hostfile
# Loaded plugins: branch, fastestmirror, langpacks
# docker-ce.x86_64 17.03.1.ce-1.el7.centos docker-ce-stable
# docker-ce.x86_64 17.03.1.ce-1.el7.centos @docker-ce-stable
# docker-ce.x86_64 17.03.0.ce-1.el7.centos docker-ce-stable
# Available Packages
# Step2: 安装指定版本的Docker-CE: (VERSION例如上面的17.03.0.ce.1-1.el7.centos)
# sudo yum -y install docker-ce-[VERSION]
#
yum -y install docker-ce-17.09.1.ce-1.el7.centos
部署master 节点
a, 配置自签证书CA
1 , 创建目录
[root@k8s-master1 ~]# mkdir -p ca/k8s
[root@k8s-master1 ~]# cd ca/k8s
2, 自签证书颁发机构(CA)
[root@k8s-master k8s]# vim ca-config.json
{"signing": {"default": {"expiry": "87600h"},"profiles": {"kubernetes": {"expiry": "87600h","usages": ["signing","key encipherment","server auth","client auth"]}}}
}[root@k8s-master k8s]# vim ca-csr.json
{"CN": "kubernetes","key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "Beijing","ST": "Beijing","O": "k8s","OU": "System"}]
}3, 生成证书
[root@k8s-master1 k8s]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -# 会生成ca.pem和ca-key.pem文件
b, 使用自签CA 签发kube-apiserver https 证书
1, 创建证书申请文件
[root@k8s-master1 k8s]# vim server-csr.json
{"CN": "kubernetes","hosts": ["10.0.0.1","127.0.0.1","192.168.6.20","192.168.6.21","192.168.6.22","192.168.6.111","192.168.6.23","192.168.6.24","192.168.6.25","kubernetes","kubernetes.default","kubernetes.default.svc","kubernetes.default.svc.cluster","kubernetes.default.svc.cluster.local"],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing","O": "k8s","OU": "System"}]
}2, 生成证书
[root@k8s-master1 k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes server-csr.json | cfssljson -bare server## 会生成server.pem和server-key.pem文件
c, 下载二进制文件,解压并安装
# 国内快速下载地址,把相应版本号替换下即可!!!
wget https://dl.k8s.io/v1.20.4/kubernetes-server-linux-amd64.tar.gz1, 创建目录
[root@k8s-master1 k8s]# cd ~
[root@k8s-master1 ~]# mkdir -p /opt/kubernetes/{bin,cfg,ssl,logs}2, 解压二进制包
[root@k8s-master1 ~]# tar -zxvf kubernetes-server-linux-amd64.tar.gz3, 拷贝(优化安装包)
[root@k8s-master1 ~]# cd kubernetes/server/bin
[root@k8s-master1 bin]# cp kube-apiserver kube-scheduler kube-controller-manager /opt/kubernetes/bin
[root@k8s-master1 bin]# cp kubectl /usr/bin/
d, 部署kube-apiserver
1, 创建配置文件
[root@k8s-master1 bin]# vim /opt/kubernetes/cfg/kube-apiserver.conf
KUBE_APISERVER_OPTS="--logtostderr=false \\
--v=2 \\
--log-dir=/opt/kubernetes/logs \\
--etcd-servers=https://192.168.6.20,https://192.168.6.20:2379,https://192.168.6.21:2379,https://192.168.6.22:2379,https://192.168.6.23:2379 \\
--bind-address=192.168.6.20 \\
--secure-port=6443 \\
--advertise-address=192.168.6.20 \\
--allow-privileged=true \\
--service-cluster-ip-range=10.0.0.0/24 \\
--enable-admission-plugins=NamespaceLifecycle,LimitRanger,ServiceAccount,ResourceQuota,NodeRestriction \\
--authorization-mode=RBAC,Node \\
--enable-bootstrap-token-auth=true \\
--token-auth-file=/opt/kubernetes/cfg/token.csv \\
--service-node-port-range=30000-32767 \\
--kubelet-client-certificate=/opt/kubernetes/ssl/server.pem \\
--kubelet-client-key=/opt/kubernetes/ssl/server-key.pem \\
--tls-cert-file=/opt/kubernetes/ssl/server.pem \\
--tls-private-key-file=/opt/kubernetes/ssl/server-key.pem \\
--client-ca-file=/opt/kubernetes/ssl/ca.pem \\
--service-account-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--service-account-issuer=api \\
--service-account-signing-key-file=/opt/kubernetes/ssl/server-key.pem \\
--etcd-cafile=/opt/etcd/ssl/ca.pem \\
--etcd-certfile=/opt/etcd/ssl/server.pem \\
--etcd-keyfile=/opt/etcd/ssl/server-key.pem \\
--requestheader-client-ca-file=/opt/kubernetes/ssl/ca.pem \\
--proxy-client-cert-file=/opt/kubernetes/ssl/server.pem \\
--proxy-client-key-file=/opt/kubernetes/ssl/server-key.pem \\
--requestheader-allowed-names=kubernetes \\
--requestheader-extra-headers-prefix=X-Remote-Extra- \\
--requestheader-group-headers=X-Remote-Group \\
--requestheader-username-headers=X-Remote-User \\
--enable-aggregator-routing=true \\
--audit-log-maxage=30 \\
--audit-log-maxbackup=3 \\
--audit-log-maxsize=100 \\
--audit-log-path=/opt/kubernetes/logs/k8s-audit.log"参考说明
• --logtostderr:启用日志
• ---v:日志等级
• --log-dir:日志目录
• --etcd-servers:etcd集群地址
• --bind-address:监听地址
• --secure-port:https安全端口
• --advertise-address:集群通告地址
• --allow-privileged:启用授权
• --service-cluster-ip-range:Service虚拟IP地址段
• --enable-admission-plugins:准入控制模块
• --authorization-mode:认证授权,启用RBAC授权和节点自管理
• --enable-bootstrap-token-auth:启用TLS bootstrap机制
• --token-auth-file:bootstrap token文件
• --service-node-port-range:Service nodeport类型默认分配端口范围
• --kubelet-client-xxx:apiserver访问kubelet客户端证书
• --tls-xxx-file:apiserver https证书
• 1.20版本必须加的参数:--service-account-issuer,--service-account-signing-key-file
• --etcd-xxxfile:连接Etcd集群证书
• --audit-log-xxx:审计日志
• 启动聚合层相关配置:--requestheader-client-ca-file,--proxy-client-cert-file,--proxy-client-key-file,--requestheader-allowed-names,--requestheader-extra-headers-prefix,--requestheader-group-headers,--requestheader-username-headers,--enable-aggregator-routing2, 拷贝刚才生成的证书
[root@k8s-master1 bin]# cp ~/ca/k8s/ca*pem ~/ca/k8s/server*pem /opt/kubernetes/ssl/
e, 启用 TLS Bootstrapping 机制
1, 配置token文件
[root@k8s-master1 bin]# vim /opt/kubernetes/cfg/token.csv
593af28f81d67e9070c97be4b65cbe20,kubelet-bootstrap,10001,"system:node-bootstrapper"2, 注:上述token可自行生成替换,但一定要与后续配置对应
head -c 16 /dev/urandom | od -An -t x | tr -d ' '
f, systemd管理apiserver
1, 创建控制文件
[root@k8s-master1 bin]# vim /usr/lib/systemd/system/kube-apiserver.service
[Unit]
Description=Kubernetes API Server
Documentation=https://github.com/kubernetes/kubernetes[Service]
EnvironmentFile=/opt/kubernetes/cfg/kube-apiserver.conf
ExecStart=/opt/kubernetes/bin/kube-apiserver $KUBE_APISERVER_OPTS
Restart=on-failure[Install]
WantedBy=multi-user.target2, 启动并设置开机启动
systemctl daemon-reload
systemctl enable kube-apiserver
systemctl start kube-apiserver
g ,部署kube-controller-manager
1, 配置文件
1, 创建配置文件
[root@k8s-master1 bin]# vim /opt/kubernetes/cfg/kube-controller-manager.conf
KUBE_CONTROLLER_MANAGER_OPTS="--logtostderr=false \\
--v=2 \\
--log-dir=/opt/kubernetes/logs \\
--leader-elect=true \\
--kubeconfig=/opt/kubernetes/cfg/kube-controller-manager.kubeconfig \\
--bind-address=127.0.0.1 \\
--allocate-node-cidrs=true \\
--cluster-cidr=10.244.0.0/16 \\
--service-cluster-ip-range=10.0.0.0/24 \\
--cluster-signing-cert-file=/opt/kubernetes/ssl/ca.pem \\
--cluster-signing-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--root-ca-file=/opt/kubernetes/ssl/ca.pem \\
--service-account-private-key-file=/opt/kubernetes/ssl/ca-key.pem \\
--experimental-cluster-signing-duration=87600h0m0s" #证书过期时间10年参数说明
• --kubeconfig:连接apiserver配置文件
• --leader-elect:当该组件启动多个时,自动选举(HA)
• --cluster-signing-cert-file/--cluster-signing-key-file:自动为kubelet颁发证书的CA,与apiserver保持一致
2, 生成证书
[root@k8s-master1 bin]# cd ~/ca/k8s/[root@k8s-master1 k8s]# vim kube-controller-manager-csr.json
{"CN": "system:kube-controller-manager","hosts": [],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing","O": "system:masters","OU": "System"}]
}[root@k8s-master1 k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-controller-manager-csr.json | cfssljson -bare kube-controller-manager
3 生成kubeconfig文件
[root@k8s-master1 k8s]# KUBE_CONFIG="/opt/kubernetes/cfg/kube-controller-manager.kubeconfig"
[root@k8s-master1 k8s]# KUBE_APISERVER="https://192.168.6.20:6443"·终端执行(4条)
kubectl config set-cluster kubernetes \\--certificate-authority=/opt/kubernetes/ssl/ca.pem \\--embed-certs=true \\--server=${KUBE_APISERVER} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-credentials kube-controller-manager \\--client-certificate=./kube-controller-manager.pem \\--client-key=./kube-controller-manager-key.pem \\--embed-certs=true \\--kubeconfig=${KUBE_CONFIG}kubectl config set-context default \\--cluster=kubernetes \\--user=kube-controller-manager \\--kubeconfig=${KUBE_CONFIG}kubectl config use-context default --kubeconfig=${KUBE_CONFIG}
4,生成service启动文件
[root@k8s-master1 k8s]# vim /usr/lib/systemd/system/kube-controller-manager.service
[Unit]
Description=Kubernetes Controller Manager
Documentation=https://github.com/kubernetes/kubernetes[Service]
EnvironmentFile=/opt/kubernetes/cfg/kube-controller-manager.conf
ExecStart=/opt/kubernetes/bin/kube-controller-manager $KUBE_CONTROLLER_MANAGER_OPTS
Restart=on-failure[Install]
WantedBy=multi-user.target#启动并设置开机启动
systemctl daemon-reload
systemctl enable kube-controller-manager
systemctl start kube-controller-manager
部署kube-scheduler
1, 创建配置文件
[root@k8s-master1 k8s]# vim /opt/kubernetes/cfg/kube-scheduler.conf
KUBE_SCHEDULER_OPTS="--logtostderr=false \\
--v=2 \\
--log-dir=/opt/kubernetes/logs \\
--leader-elect \\
--kubeconfig=/opt/kubernetes/cfg/kube-scheduler.kubeconfig \\
--bind-address=127.0.0.1"参数说明
• --kubeconfig:连接apiserver配置文件
• --leader-elect:当该组件启动多个时,自动选举(HA)
2, 生成kube-scheduler证书
[root@k8s-master1 k8s]# cd /root/ca/k8s
[root@k8s-master1 k8s]# vim kube-scheduler-csr.json
{"CN": "system:kube-scheduler","hosts": [],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing","O": "system:masters","OU": "System"}]
}#生成证书
[root@k8s-master1 k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-scheduler-csr.json | cfssljson -bare kube-scheduler
3, 生成kubeconfig文件
[root@k8s-master1 k8s]# KUBE_CONFIG="/opt/kubernetes/cfg/kube-scheduler.kubeconfig"
[root@k8s-master1 k8s]# KUBE_APISERVER="https://192.168.6.20:6443"·终端执行(4条)
kubectl config set-cluster kubernetes \\--certificate-authority=/opt/kubernetes/ssl/ca.pem \\--embed-certs=true \\--server=${KUBE_APISERVER} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-credentials kube-scheduler \\--client-certificate=./kube-scheduler.pem \\--client-key=./kube-scheduler-key.pem \\--embed-certs=true \\--kubeconfig=${KUBE_CONFIG}kubectl config set-context default \\--cluster=kubernetes \\--user=kube-scheduler \\--kubeconfig=${KUBE_CONFIG}kubectl config use-context default --kubeconfig=${KUBE_CONFIG}
4, 生成启动文件service
[root@k8s-master1 k8s]# vim /usr/lib/systemd/system/kube-scheduler.service
[Unit]
Description=Kubernetes Scheduler
Documentation=https://github.com/kubernetes/kubernetes[Service]
EnvironmentFile=/opt/kubernetes/cfg/kube-scheduler.conf
ExecStart=/opt/kubernetes/bin/kube-scheduler $KUBE_SCHEDULER_OPTS
Restart=on-failure[Install]
WantedBy=multi-user.target#启动并设置开机启动
systemctl daemon-reload
systemctl enable kube-scheduler
systemctl start kube-scheduler
查看集群状态
1, 生成kubectl连接集群的证书
cd /root/ca/k8s
[root@k8s-master1 k8s]# vim admin-csr.json
{"CN": "admin","hosts": [],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing","O": "system:masters","OU": "System"}]
}[root@k8s-master1 k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes admin-csr.json | cfssljson -bare admin
2,生成kubeconfig文件
[root@k8s-master1 k8s]# mkdir /root/.kube[root@k8s-master1 k8s]# KUBE_CONFIG="/root/.kube/config"
[root@k8s-master1 k8s]# KUBE_APISERVER="https://192.168.6.20:6443"·终端执行(4条)
kubectl config set-cluster kubernetes \\--certificate-authority=/opt/kubernetes/ssl/ca.pem \\--embed-certs=true \\--server=${KUBE_APISERVER} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-credentials cluster-admin \\--client-certificate=./admin.pem \\--client-key=./admin-key.pem \\--embed-certs=true \\--kubeconfig=${KUBE_CONFIG}kubectl config set-context default \\--cluster=kubernetes \\--user=cluster-admin \\--kubeconfig=${KUBE_CONFIG}kubectl config use-context default --kubeconfig=${KUBE_CONFIG}
3,通过kubectl工具查看当前集群组件状态
root@k8s-master1 k8s]# kubectl get cs
Warning: v1 ComponentStatus is deprecated in v1.19+
NAME STATUS MESSAGE ERROR
scheduler Healthy ok
controller-manager Healthy ok
etcd-2 Healthy {"health":"true"}
etcd-0 Healthy {"health":"true"}
etcd-1 Healthy {"health":"true"}
部署worker node
部署node1
1, 安装前的软件准备
# 创建工作目录并拷贝文件
[root@k8s-node1 ~]# mkdir -p /opt/kubernetes/{bin,cfg,ssl,logs}[root@k8s-master k8s]# cd /root/ca/k8s/kubernetes/server/bin[root@k8s-master bin]# scp kubelet kube-proxy node1:/opt/kubernetes/bin/
[root@k8s-master bin]# scp kubelet kube-proxy node2:/opt/kubernetes/bin/2, 部署kubelet
pause 版本使用3.0
a, 设置配置文件
node1,node2
[root@node1 ~]# vim /opt/kubernetes/cfg/kubelet.conf
KUBELET_OPTS="--logtostderr=false \\
--v=2 \\
--log-dir=/opt/kubernetes/logs \\
--hostname-override=master1 \\ #每个节点的ip/名称
--network-plugin=cni \\
--kubeconfig=/opt/kubernetes/cfg/kubelet.kubeconfig \\
--bootstrap-kubeconfig=/opt/kubernetes/cfg/bootstrap.kubeconfig \\
--config=/opt/kubernetes/cfg/kubelet-config.yml \\
--cert-dir=/opt/kubernetes/ssl \\
--pod-infra-container-image=registry.cn-hangzhou.aliyuncs.com/google_containers/pause-amd64:3.0"
拉去镜像
node1,node2
[root@node1 ~]# docker pull lizhenliang/pause-amd64:3.0
[root@node1 ~]# docker pull registry.cn-hangzhou.aliyuncs.com/google_containers/pause-amd64:3.0
#配置参数文件
node1, node2
[root@node1 ~]# vim /opt/kubernetes/cfg/kubelet-config.yml
kind: KubeletConfiguration
apiVersion: kubelet.config.k8s.io/v1beta1
address: 0.0.0.0
port: 10250
readOnlyPort: 10255
cgroupDriver: cgroupfs
clusterDNS:
- 10.0.0.2
clusterDomain: cluster.local
failSwapOn: false
authentication:anonymous:enabled: falsewebhook:cacheTTL: 2m0senabled: truex509:clientCAFile: /opt/kubernetes/ssl/ca.pem
authorization:mode: Webhookwebhook:cacheAuthorizedTTL: 5m0scacheUnauthorizedTTL: 30s
evictionHard:imagefs.available: 15%memory.available: 100Minodefs.available: 10%nodefs.inodesFree: 5%
maxOpenFiles: 1000000
maxPods: 110#授权kubelet-bootstrap用户允许请求证书
kubectl create clusterrolebinding kubelet-bootstrap \\
--clusterrole=system:node-bootstrapper \\
--user=kubelet-bootstrap生成kubelet初次加入集群引导kubeconfig文件
*在生成kubernetes证书的目录下执行以下命令生成kubeconfig文件TOKEN=$(awk -F "," '{print $1}' /opt/kubernetes/cfg/token.csv)
其中
[root@k8s-master1 bin]# awk -F "," '{print $1}' /opt/kubernetes/cfg/token.csv
[root@k8s-master1 bin]# cd /root/ca/k8s/
[root@k8s-master1 k8s]# KUBE_CONFIG="/opt/kubernetes/cfg/bootstrap.kubeconfig"
[root@k8s-master1 k8s]# KUBE_APISERVER="https://192.168.6.20:6443" # apiserver的 IP:PORT
[root@k8s-master1 k8s]# TOKEN="593af28f81d67e9070c97be4b65cbe20" # 与master的token.csv里保持一致·终端执行(四条)
kubectl config set-cluster kubernetes \\--certificate-authority=/opt/kubernetes/ssl/ca.pem \\--embed-certs=true \\--server=${KUBE_APISERVER} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-credentials "kubelet-bootstrap" \\--token=${TOKEN} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-context default \\--cluster=kubernetes \\--user="kubelet-bootstrap" \\--kubeconfig=${KUBE_CONFIG}kubectl config use-context default --kubeconfig=${KUBE_CONFIG}# node1
[root@k8s-master1 k8s]#scp /opt/kubernetes/ssl/ca.pem node1:/opt/kubernetes/ssl/
[root@k8s-master1 k8s]#scp /opt/kubernetes/cfg/bootstrap.kubeconfig root@node1:/opt/kubernetes/cfg/#node2
[root@k8s-master1 k8s]#scp /opt/kubernetes/ssl/ca.pem node2:/opt/kubernetes/ssl/
[root@k8s-master1 k8s]#scp /opt/kubernetes/cfg/bootstrap.kubeconfig root@node2:/opt/kubernetes/cfg/[root@k8s-master1 k8s]#kubectl create clusterrolebinding kubelet-bootstrap --clusterrole=system:node-bootstrapper --user=kubelet-bootstrapnode1, node2
#systemd管理kubelet
[root@k8s-master1 k8s]# vim /usr/lib/systemd/system/kubelet.service
[Unit]
Description=Kubernetes Kubelet
After=docker.service[Service]
EnvironmentFile=/opt/kubernetes/cfg/kubelet.conf
ExecStart=/opt/kubernetes/bin/kubelet $KUBELET_OPTS
Restart=on-failure
LimitNOFILE=65536[Install]
WantedBy=multi-user.target#启动并设置开机启动
systemctl daemon-reload
systemctl enable kubelet1
systemctl start kubelet1在Master1上批准新Node kubelet证书申请
1, 查看证书请求
[root@k8s-master1 cfg]# kubectl get csr
2, 授权请求(Pending,一定要是待定状态的)
[root@k8s-master1 cfg]# kubectl certificate approve node-csr-xQsFeNF5nlB-rZQr2cIxFB18ET3kAGYHSC9GMSKDoI83, 查看Node状态
[root@k8s-master1 cfg]# kubectl get node
3, 部署kube-proxy
a, 生成请求证书
在master1 节点下
#在/root/ca/k8s下创建证书请求文件
cd /root/ca/k8s
s-master1 k8s]# vim kube-proxy-csr.json
{"CN": "system:kube-proxy","hosts": [],"key": {"algo": "rsa","size": 2048},"names": [{"C": "CN","L": "BeiJing","ST": "BeiJing","O": "k8s","OU": "System"}]
}# 生成证书
[root@k8s-master1 k8s]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes kube-proxy-csr.json | cfssljson -bare kube-proxy
##生成证书 kube-proxy-key.pem kube-proxy.pem#生成kubeconfig文件
[root@k8s-master1 k8s]# KUBE_CONFIG="/opt/kubernetes/cfg/kube-proxy.kubeconfig"
[root@k8s-master1 k8s]# KUBE_APISERVER="https://192.168.6.20:6443"·终端执行(4条)
kubectl config set-cluster kubernetes \\--certificate-authority=/opt/kubernetes/ssl/ca.pem \\--embed-certs=true \\--server=${KUBE_APISERVER} \\--kubeconfig=${KUBE_CONFIG}kubectl config set-credentials kube-proxy \\--client-certificate=./kube-proxy.pem \\--client-key=./kube-proxy-key.pem \\--embed-certs=true \\--kubeconfig=${KUBE_CONFIG}kubectl config set-context default \\--cluster=kubernetes \\--user=kube-proxy \\--kubeconfig=${KUBE_CONFIG}kubectl config use-context default --kubeconfig=${KUBE_CONFIG}
主要是为了生成kube-proxy.kubeconfig文件的,并将其复制到node 节点scp /opt/kubernetes/cfg/kube-proxy.kubeconfig root@node1:/opt/kubernetes/cfg/scp /opt/kubernetes/cfg/kube-proxy.kubeconfig root@node2:/opt/kubernetes/cfg/
b, 配置文件
node1, node2
#创建配置文件
vim /opt/kubernetes/cfg/kube-proxy.conf
KUBE_PROXY_OPTS="--logtostderr=false \\
--v=2 \\
--log-dir=/opt/kubernetes/logs \\
--config=/opt/kubernetes/cfg/kube-proxy-config.yml"#配置参数文件
vim /opt/kubernetes/cfg/kube-proxy-config.yml
kind: KubeProxyConfiguration
apiVersion: kubeproxy.config.k8s.io/v1alpha1
bindAddress: 0.0.0.0
metricsBindAddress: 0.0.0.0:10249
clientConnection:kubeconfig: /opt/kubernetes/cfg/kube-proxy.kubeconfig
hostnameOverride: master1
clusterCIDR: 10.244.0.0/16# 注意需要修改的地方hostnameOverride: node1或是node2
3, systemd管理kube-proxy
vim /usr/lib/systemd/system/kube-proxy.service
[Unit]
Description=Kubernetes Proxy
After=network.target[Service]
EnvironmentFile=/opt/kubernetes/cfg/kube-proxy.conf
ExecStart=/opt/kubernetes/bin/kube-proxy $KUBE_PROXY_OPTS
Restart=on-failure
LimitNOFILE=65536[Install]
WantedBy=multi-user.target#启动并设置开机启动
systemctl daemon-reload
systemctl enable kube-proxy
systemctl start kube-proxy
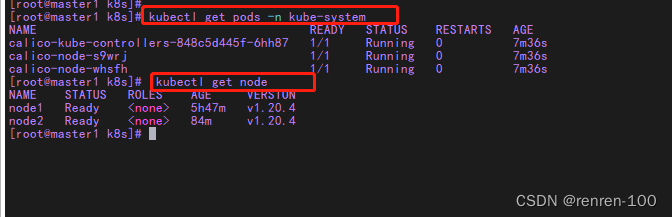
4, 部署网络组件calico
calico 适用版本需要查看官网
官方地址
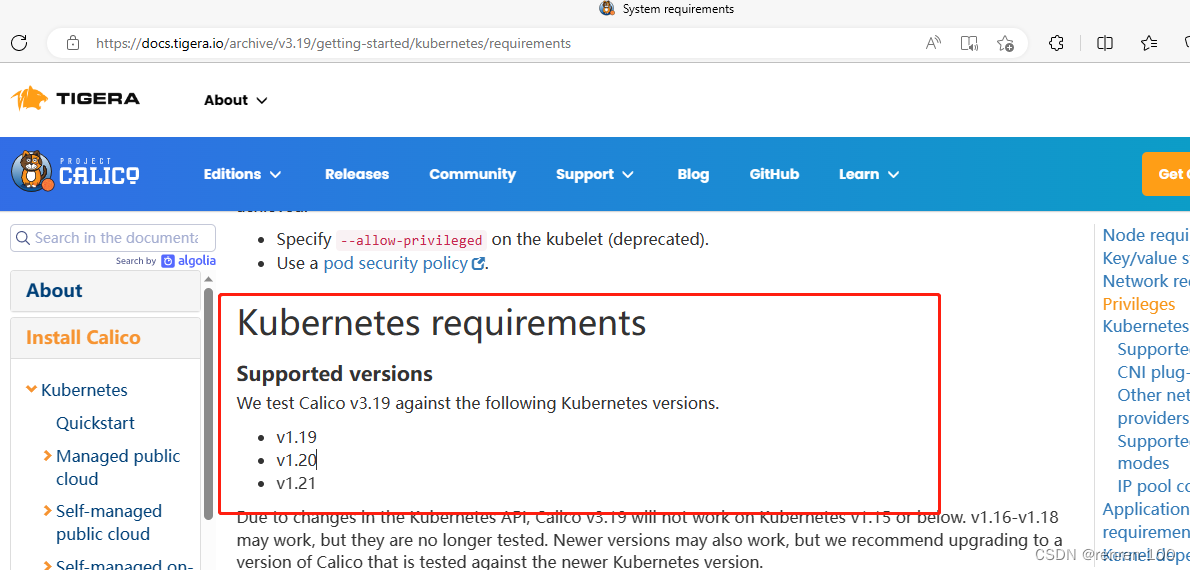
wget https://docs.projectcalico.org/archive/v3.19/manifests/calico.yaml --no-check-certificate1, #部署Calico
[root@k8s-master1 k8s]# cd /opt/kubernetes/cfg/
*上传至/opt/kubernetes/cfg/[root@k8s-master1 cfg]# kubectl apply -f calico.yaml
[root@k8s-master1 cfg]# kubectl get pods -n kube-system等Calico Pod都Running,节点也会准备就绪
可能有点久,要初始化创建对应镜像,好几分钟
waiting......................
5, 部署coredns
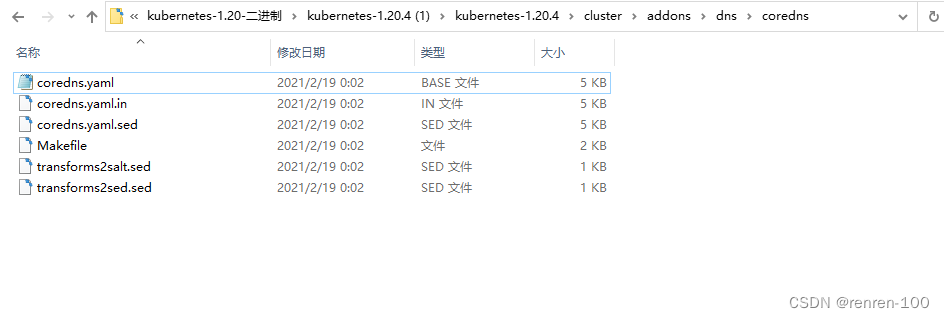
下载地址
github下载kubernetes
coredns.yaml 来源
修改配置
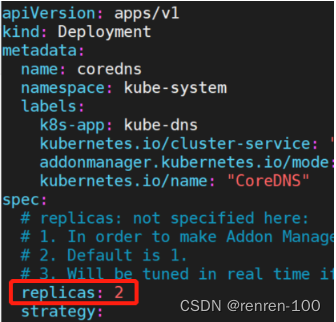
注意需要修改coredns.yaml 中的参数:
memory: 170Mi
image: coredns/coredns:版本号 #指定镜像下载地址
clusterIP 10.0.0.2 #指定clusterip
kubernetes cluster.local in-addr.arpa ip6.arpa
根据需要还可以设置 Deployment.spec.replicas:
如果负载压力比较大,除了调整cpu,memory的资源,还可以扩大副本数,在yaml文件中, 添加副本参数,设置为两个副本
kubectl apply -f coredns.yaml#源码包https://github.com/coredns/coredns/releases/tag/v1.2.2
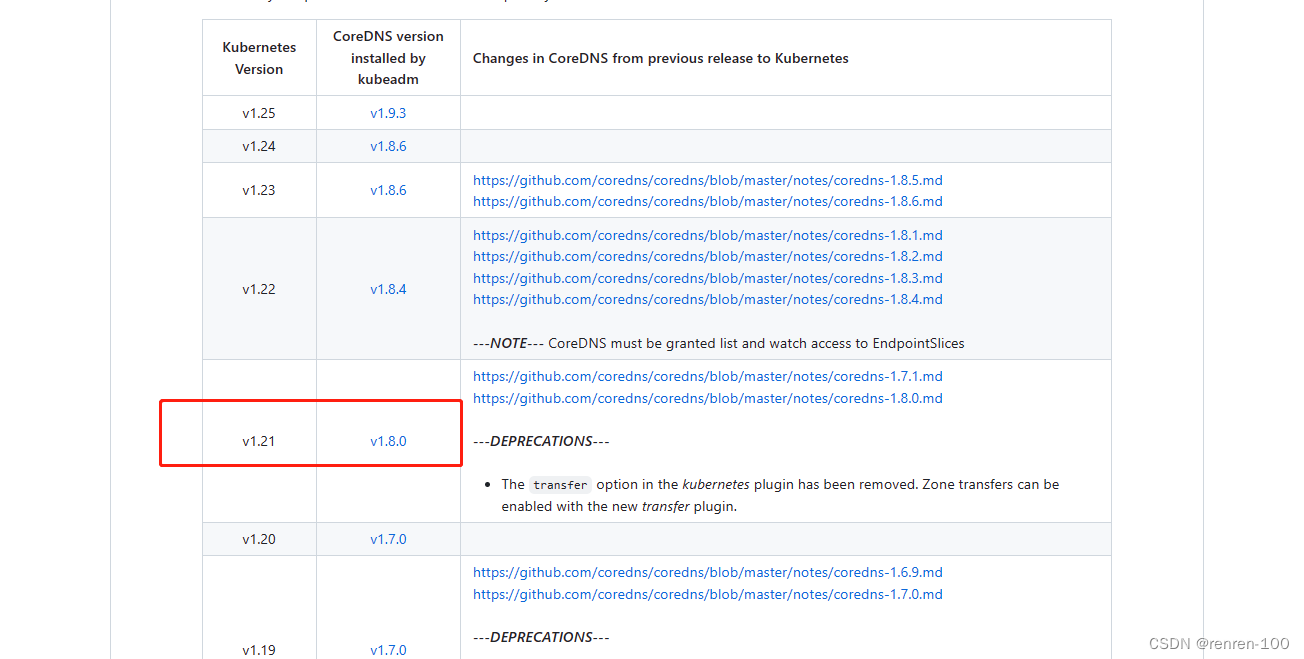
kubenetes官网对应的coredns版本
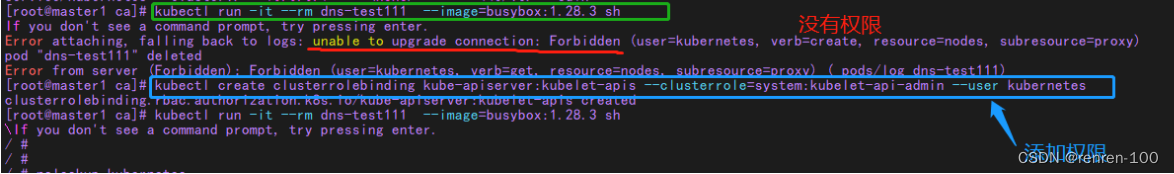
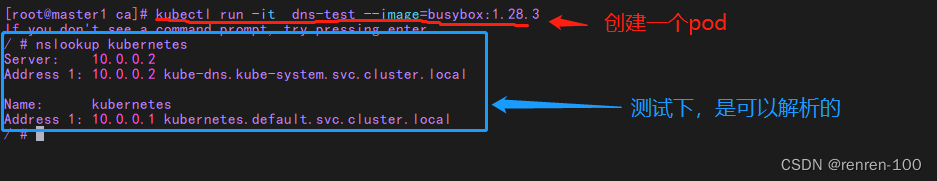
测试
# 期间执行时有报错,添加权限
[root@k97 work]# kubectl create clusterrolebinding kube-apiserver:kubelet-apis --clusterrole=system:kubelet-api-admin --user kubernetes
clusterrolebinding.rbac.authorization.k8s.io/kube-apiserver:kubelet-apis createdkubectl run -it dns-test --image=busybox:1.28.3 sh
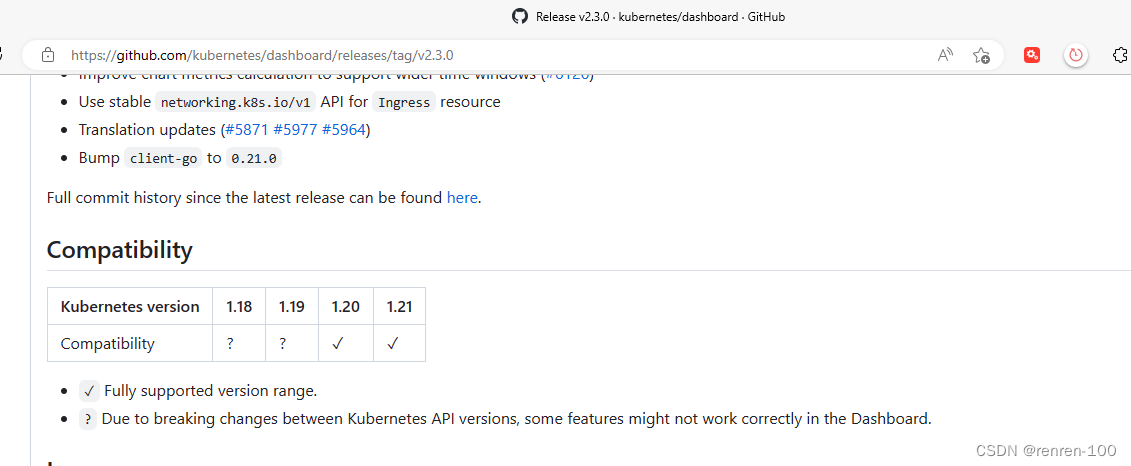
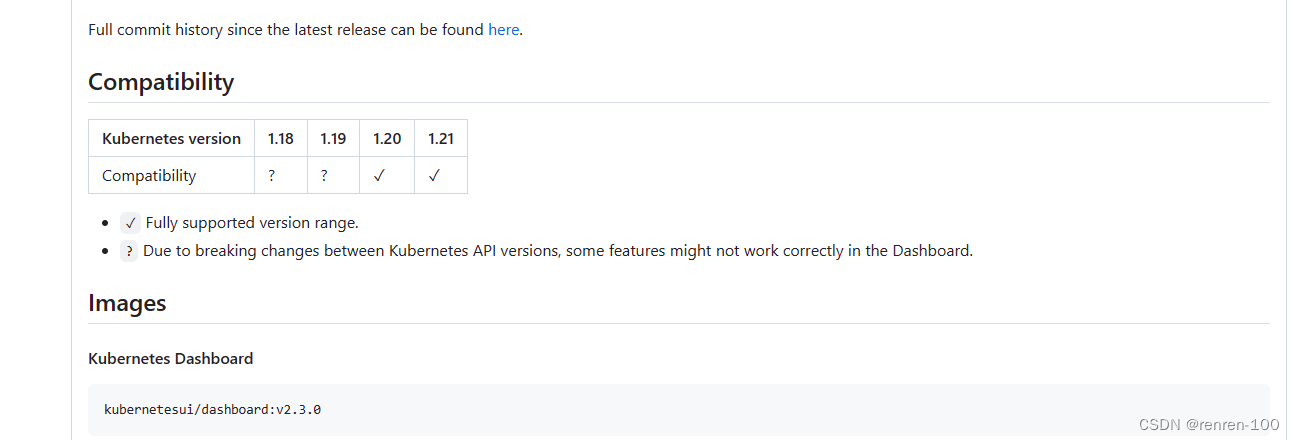
dashboard 安装部署
有两种手段确定具体安装那一版本的dashboard ,一个是下载对应版本的kubernetes Github上的源码包
另一个是通过github上的文档,链接见参考资料1
安装
在对应kubernetes源码包中有对应的dashboard.yaml 文件,具体路径:下载包下kubernetes-1.20.4\\cluster\\addons\\dashboard
github下载链接
参考资料1
参考资料2
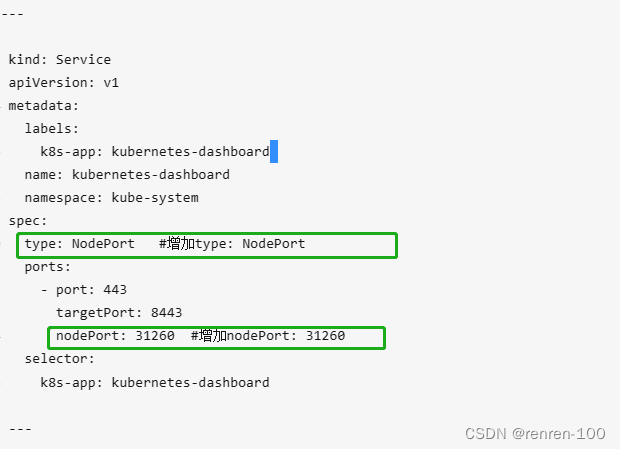
首先
在Service资源配置中将type 改为 type: NodePort
spec.type: NodePort
spec.ports.nodePort: 31260然后
kubectl apply -f dashboard.yaml
其次
kubectl get all -n kubernetes-dashboard最后 https://NodeIP:nodeport 登录图形化界面
配置token认证
# 创建用于登陆dashboard的ServiceAccount首先创建一个叫admin-user的服务账号,并放在kubernetes-dashboard名称空间kubectl create serviceaccount admin-user -n kubernetes-dashboard其次通过绑定clusterrole授权kubectl create clusterrolebinding admin-user --clusterrole=cluster-admin --serviceaccount=kubernetes-dashboard:admin-user``然后 查看 admin-user的token
a=$(kubectl -n kubernetes-dashboard get secret|awk '/^admin-user/{print $1}')最后 查看admin-user的token
kubectl describe secrets $a -n kubernetes-dashboard
或者是
kubectl get secret $a -n kubernetes-dashboard -o jsonpath={.data.token}|base64 -d配置kubeconfig文件
kubectl describe secrets admin-user-token-7r8t5 -n kubernetes-dashboardDASH_TOCKEN=$(kubectl get secret admin-user-token-7r8t5 -n kubernetes-dashboard -o jsonpath={.data.token}|base64 -d)
# 1,创建cluster集群
kubectl config set-cluster kubernetes --certificate-authority=/root/ca/k8s/ca.pem --server="https://192.168.6.20:6443" --embed-certs=true --kubeconfig=/root/dashboard-admin.conf# 2,创建credentials
DASH_TOCKEN=$(kubectl get secret admin-user-token-7r8t5 -n kubernetes-dashboard -o jsonpath={.data.token}|base64 -d)kubectl config set-credentials dashboard-admin --token=$DASH_TOCKEN --kubeconfig=/root/dashboard-admin.conf# 3,创建context
kubectl config set-context dashboard-admin@kubernetes --cluster=kubernetes --user=dashboard-admin --kubeconfig=/root/dashboard-admin.conf# 4, 切换context的current-context
kubectl config use-context dashboard-admin@kubernetes --kubeconfig=/root/dashboard-admin.conf
把dashboard-admin.conf文件下载到电脑桌面,上传到kubeconfig处登录即可
k8s 官方文档
https://kubernetes.io/docs/tasks/administer-cluster/access-cluster-api/